A digital forensic imager can be in the form of a software imaging tool or hardware equipment. A good forensic imaging tool can output to several forensics formats and is commonly used by law enforcement agencies, private investigation firms, and security companies nowadays.
Below is a quick summary of the best forensic imagers and their imaging capability.
| S/no | Forensic Imaging Tool | Description | Type |
|---|---|---|---|
| 1 | FTK® Imager | Computer imaging | Software |
| 2 | Tableau Forensic Imager (TX1) | Computer imaging | Hardware |
| 3 | EnCase™ Forensic | Computer imaging | Software |
| 4 | SIFT Workstation | Computer imaging | Software |
| 5 | Magnet RAM Capture | RAM imaging | Software |
| 6 | Magnet ACQUIRE | Computer & Mobile imaging | Software |
| 7 | Cellebrite UFED | Mobile device imaging | Software and Hardware |
What is a Forensic Image?
A forensic image is a court-accepted digital image of a digital device or a digital file, such as a computer, a mobile phone or a system drive. It is considered forensically sound as the forensic image is a bit-by-bit copy of the original device, drive or file.
A forensic image is acquired using specialized digital forensics software or hardware equipment and is examined primarily by digital forensics analysis tools.
What are the Different Formats of Forensic Images?
The most common forensic image formats being used are;
- EnCase Evidence Files = E01 / Ex01
- Raw Format = dd
- Advance Forensics Format = AFF
What are the BEST Forensic Imaging Software Tools?
Here are the seven (7) best digital forensics imaging tools you can use.
1. FTK® Imager
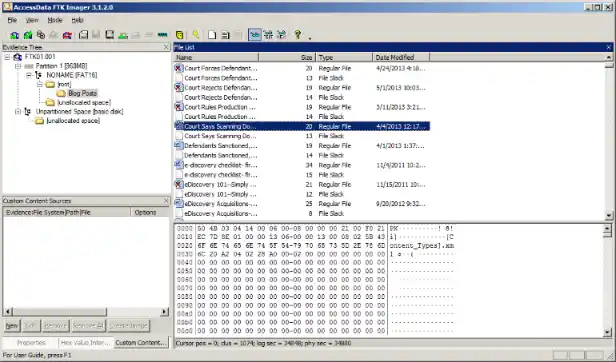
FTK® Imager is a data preview and imaging software tool that allows you to quickly assess electronic evidence to determine if further analysis using forensic tools is needed.
The imaging tool can make forensic copies of physical disks, logical drives, individual files, entire folders, discs, USB flash drives, etc.
FTK Imager – Key Features
- Create perfect or forensic copies from the original.
- Generate hash reports before and after the forensic image is created
- Ability to mount images as read-only
2. Tableau Forensic Imager (TX1)

Measuring 9.5 in (L) x 6.5 in (W) x 2.6 in (H), the Tableau Forensic Imager (TX1) is a physical forensic imager hardware device that is used to create forensic images of a wide range of computer media, including USB flash drives, SATA hard drives, PCIe and 10Gb Ethernet devices.
When TX1 starts imaging, it can output to raw DD formats, .e01 (compressed) or .ex01 (compressed), and supports a wide range of file systems, such as ExFAT, NTFS, EXT4, FAT32, HFS+ and many more.
TX1 – Key Features
- Support up to two active forensic jobs simultaneously
- Pause and resume imaging jobs
- Automatic job queuing allows additional jobs to begin as soon as an active job completes
- Secure Wiping and Formatting features
- AES whole disk encryption
3. EnCase™ Forensic
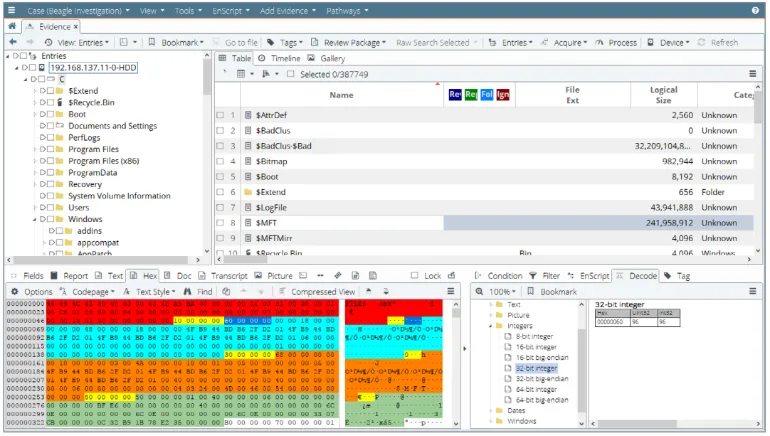
EnCase™ Forensic is a software imaging tool used by the majority of law enforcement agencies in the world. The strength of this forensic imaging software lies in its competency in acquiring forensic images from a wide array of computer systems.
It is especially good at analyzing Windows operating systems and commonly-used file systems such as NTFS, FAT/FAT32/exFAT/, ext4 and many more.
EnCase Forensics – Key Features
- Analyze data from multiple platforms—Windows, Linux, AIX, OS X, Solaris, and more
- Uncover suspicious files, e.g. hiding, cloaking, or deletion
- Manage large data volume, including deleted files, unallocated space and file slack.
- Indexing, keyword searching and automated evidence-processing features
- Create exact forensic duplicates through verifiable hash values and Cyclic Redundancy Check (CRC) values
- Easy transfer of evidence files to external parties, such as legal representatives
4. SIFT Workstation
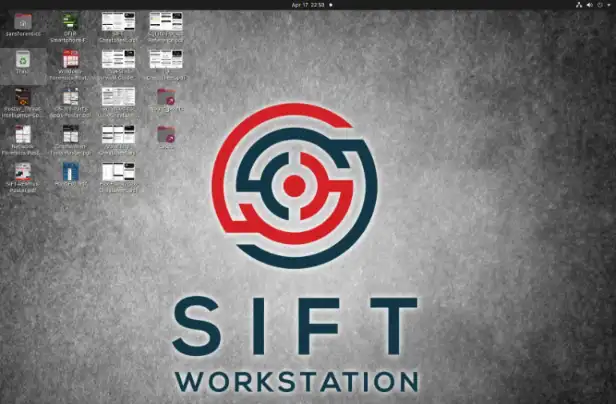
SIFT Workstation is a software imaging VMware appliance, pre-configured with free, open-source forensics and analysis tools to perform deep digital forensic investigations in various environments.
It can image attached physical devices and system drives using a range of forensic command formats, such as raw dd, E01, AFF, etc.
SIFT Workstation – Key Features
- Lots of installed forensic applications, e.g. log2timeline
- Mounting of raw and forensic images
- Conduct forensic investigation using installed suites like the sleuthkit.
- Conduct incident response investigations
5. Magnet RAM Capture
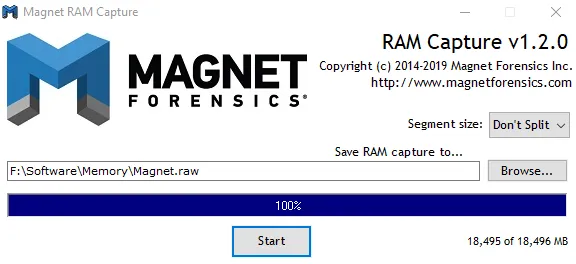
Magnet RAM Capture is a software imaging tool that can recover and examine artefacts frequently found only in the memory by taking a snapshot of a suspect’s computer’s physical memory (RAM).
You can use Magnet RAM Capture while minimizing memory overwriting thanks to its minimal memory footprint. Furthermore, you can transfer the memory data into analysis programs like Magnet AXIOM after you have captured it.
6. Magnet ACQUIRE
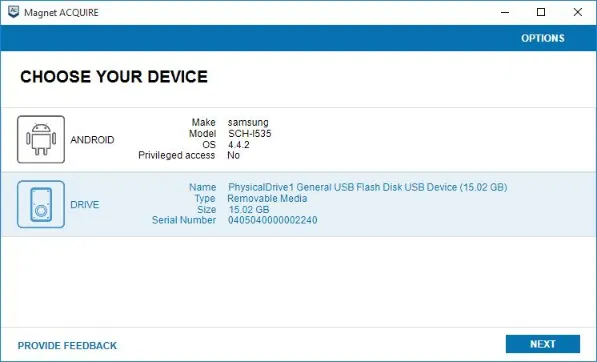
Magnet ACQUIRE is a software imaging tool capable of mobile device image acquisition and capturing forensic images of common storage drives, including hard drives and USB flash drives.
The forensic acquisition tool can output the image to the E01 and raw dd format.
For mobile devices, depending on the make & model of the device, it can acquire a logical extraction, file system extraction or even a full physical image extraction.
Magnet ACQUIRE – Key Features
- Use Media Transfer Protocol to acquire media and files, such as photos, videos and documents from mobile devices.
- Support 3rd-party application user data
- Support extraction of memory cards, e.g. microSD cards
7. Cellebrite UFED
Cellebrite is an Israeli digital intelligence company focusing mainly on extracting data from mobile devices. The forensic image it outputs is in its proprietary form, the UFDR format.
The UFED capability is available on desktop computers (UFED4PC) as software, as well as a standalone handheld physical console (UFED Touch2).
Cellebrite UFED – Key Features
- Unlocking of mobile devices via pattern bypass and PIN locks
- Perform logical, file system and physical extractions
- Use of bootloaders, automatic EDL capability, smart ADB connection and more
- Wide range of supported mobile devices across many different brands
- Extract evidence from mobile phones, SIM cards, drones, SD cards, GPS devices and more