The field of digital forensics is used by law enforcement agencies when it comes to criminal investigations to extract evidence, as well as in the private sector, where incidents such as data breaches, litigation, inside threats, fraud, etc., require the need for forensics investigations to find out the truth.
The sub-discipline of digital forensics includes mobile forensics, cloud forensics, memory forensics and many more.
Every digital forensics tool has its own strengths when it comes to examining the different types of devices. There are always specific forensic tools that cater for a specific operating system.
Not to be confused with data recovery, the four (4) steps involved in a digital forensics scientific methodology begin with;
| Steps | Stage/s | Comments |
|---|---|---|
| 1 | Collection | The proper seizure procedure of devices to prevent physical damage and/or file contamination |
| 2 | Preservation | The forensic process of acquiring (imaging) a forensic image of the device |
| 3 | Analysis | The examination stage to uncover any inculpatory or exculpatory digital evidence using digital forensic tools |
| 4 | Presentation | Explaining the forensic findings, typically presented in a court of law when used by law enforcement agencies |
List of the Best Digital Forensics software
Depending on the type of device and operating system you are acquiring, we can choose the best digital forensics tools for each sub-discipline of digital forensics.
1. EnCase Forensic
Court-proven computer forensic tool used by law enforcement around the world
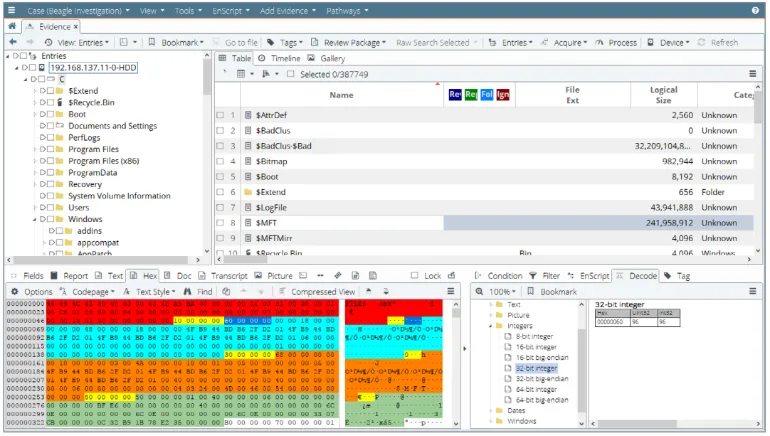
Starting in the early days of 1998, EnCase is the pioneer in the field of computer forensics when it comes to criminal investigations and analysis.
Used by the majority of law enforcement agencies in the world, the strength of EnCase Forensic software lies in its competency in acquiring forensic images from a wide array of computer systems. It is especially good at analysing Windows operating systems and commonly-used file systems such as NTFS, FAT/FAT32/exFAT/, ext4 and many more.
EnCase Forensic – Key Features
- Analyze data from multiple platforms—Windows, Linux, AIX, OS X, Solaris, and more
- Uncover suspicious files, e.g. hiding, cloaking, or deletion
- Manage large data volume, including deleted files, unallocated space and file slack.
- Indexing, keyword searching and automated evidence-processing features
- Create exact forensic duplicates through verifiable hash values and Cyclic Redundancy Check (CRC) values
- Easy transfer of evidence files to external parties, such as legal representatives
2. Cellebrite UFED
Since entering the mobile forensics industry in 2007, Cellebrite UFED has been the leading market leader in this space for many years.
Cellebrite is an Israeli digital intelligence company focusing mainly on extracting data from mobile devices. The company has several offices across the world, including Washington D.C, Germany and Singapore.
The UFED capability is available on platforms such as desktop computers (UFED4PC) and a standalone handheld console (UFED Touch2).
Cellebrite UFED – Key Features
- Unlocking of mobile devices via pattern bypass and PIN locks
- Perform logical, file system and physical extractions
- Use of bootloaders, automatic EDL capability, smart ADB connection and more
- Wide range of supported mobile devices across many different brands
- Extract evidence from mobile phones, SIM cards, drones, SD cards, GPS devices and more
3. SIFT Workstation
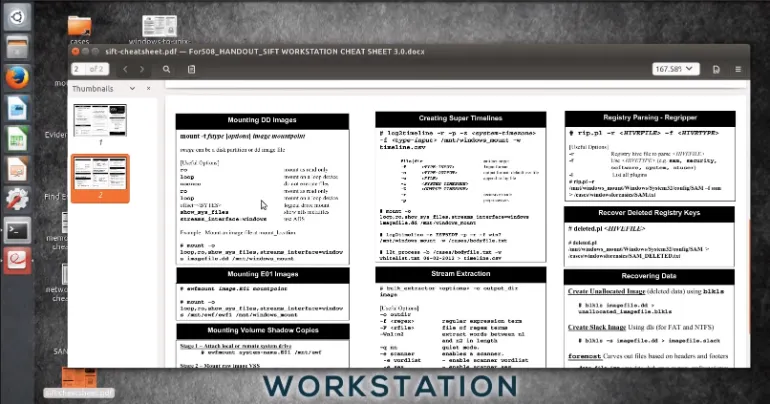
Created in 2007 by Rob Lee from SANS Institute, the SIFT Workstation is a free Linux Ubuntu distro that is packed with open-source digital forensics and incident response tools.
SIFT is designed to perform detailed digital forensic examinations and incident response capabilities, typically on computer systems. Most of the forensic tools installed onto SIFT requires some form of command-line knowledge, although there are other tools with GUI interface as well, e.g. Sleuthkit.
SIFT Workstation – Key Features
- File system support for NTFS, raw, HFS+, FAT/exFAT, swap, RAM data and more
- Evidence image support for E01, raw, dd, ewf, aff, vmdk, vhd, etc
- Forensic tools installed, such as Volatility, bulk_extractor, imagemounter, libewf, Sleuthkit, RegRipper, etc
4. Sumuri Recon Lab
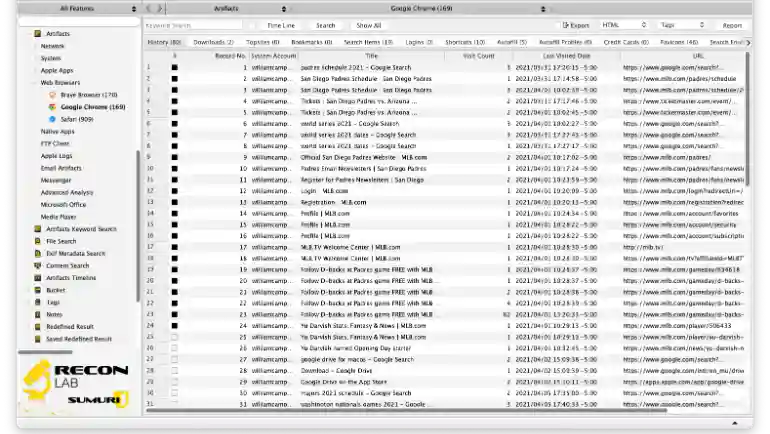
Sumuri’s flagship forensic suite is the Recon Lab. The digital forensics software can take in forensic images, mounted volumes, optical disk images, RAM images and its own RECON FS block image.
Recon is to be installed on a macOS machine, and it has several useful features such as skin tone detection, face analysis, RAM memory analysis, indexing and keyword searching.
Sumuri – Key Features
- Parse and recover thousands of artefacts with Automated Analysis of macOS, Windows, Android, iOS and Google Takeout files.
- Advanced forensic viewers for macOS plist, SQLite databases, HEX and Window’s Registry
- Timeline support for placing events in chronological order
- Advanced-Data Correlation feature
- Include Paragon’s Mac Toolbox and Linux drivers
- Integrated Report Editor
- Support over 270 unique timestamps
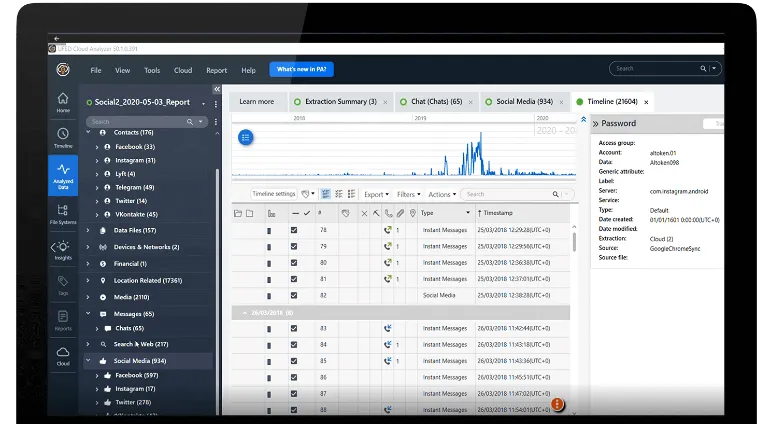
5. Oxygen Forensics
Similar to Cellebrite UFED, Oxygen Forensics is a Russian company headquartered in Alexandria, Virginia and provides mobile forensics capabilities to law enforcement, federal agencies and enterprises.
The forensic software is an all-in-one platform that can extract mobile forensic images, decode them and parse them in its interface for investigators to analyse easily. Multiple extractions can be investigated in a single Oxygen Forensic interface to have a complete picture of all the acquired data.
Oxygen Forensics – Key Features
- File system-level extraction on most mobile devices
- Drone forensics possible
- Bypass screen lock on popular Android devices
- Cloud extraction – Acquire data from cloud services and storage
- Support import of call data records
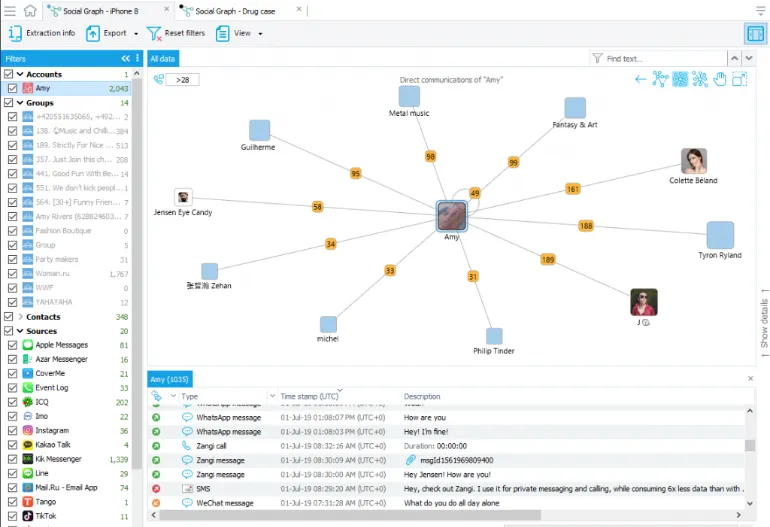
6. Magnet Axiom
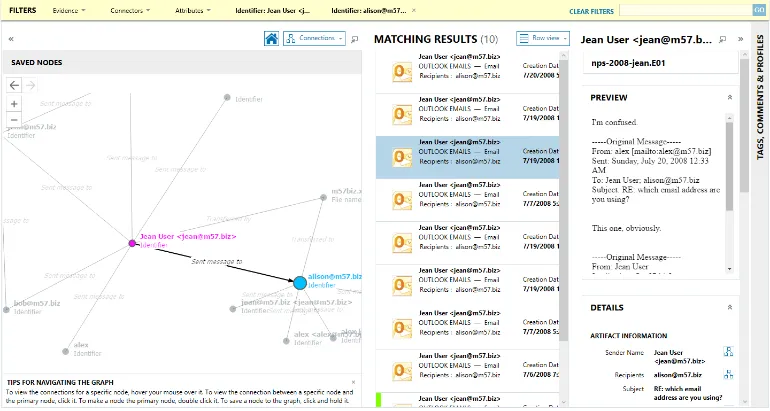
Magnet AXIOM is a forensic platform that can take in different types of forensic images (mobile, computer and cloud data), process them and present them in an analytical interface for examiners to find key evidence quickly.
The forensic tool supports the analysis of Android, iOS, Windows, macOS, Linux and extraction dumps of over 50+ cloud services.
Magnet AXIOM – Key Features
- Analyze vehicle data with support for Berla iVE extractions
- Dedicated artefacts support for most popular and relevant sources
- Built-in support for GrayKey (mobile acquisition)
- Analytics tools, such as visualizing connections between people and devices
- Reporting and Case Sharing feature
7. FTK® Forensic Toolkit
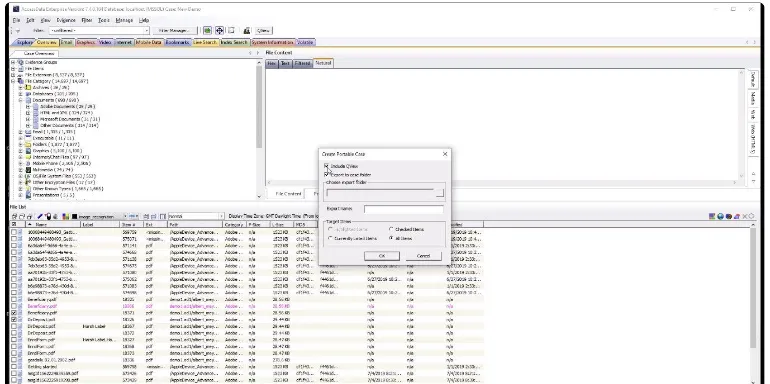
Similar to EnCase Forensic, FTK is a digital investigation solution frequently used by law enforcement and in civil cases. it is primarily used in computer forensics and is well-regarded in terms of its fast processing speed and intuitive interface. It uses distributed processing and true multi-threaded/multi-core support to ingest large amounts of digital data.
FTK Forensic Toolkit is a full disk image collection, processing and analysis solution that parses data in a forensically-sound manner. This allows investigators to preserve the integrity of the data while utilizing time to analyze files and perform advanced deep dives in areas such as data craving and file decryption.
FTK – Key Features
- Email Analysis
- Customizable data views
- Indexing upfront so searching and filtering are faster subsequently
- Ability to train FTK for facial and image recognition
- Ability to create custom Python scripts
Bonus
Mac Target Disk Mode

Apple has a built-in “Target Disk Mode” feature for all their Mac series of computers. Mac users can boot into this unique startup mode that enables them to perform data transfers from one Mac to another.
The condition here is you must have two (2) Mac computers.
The Mac you initiated in the target disk mode will act as an external hard drive for the other Mac.
To begin target disk mode, do the following steps;
- Connect the two (2) Macs with the same cable (e.g. USB C or Thunderbolt)
- Decide on the Mac that you want to act as an external drive
- If the Mac is Off, start it up and long-press the T key
- If the Mac is On, click the Apple icon on the top-left > System Preferences > click Startup Disk > Click Target Disk Mode
- You can start to transfer files by dragging them once you see the disk icon
- Once done with the file transfer, eject the disk by dragging its icon to the Trash